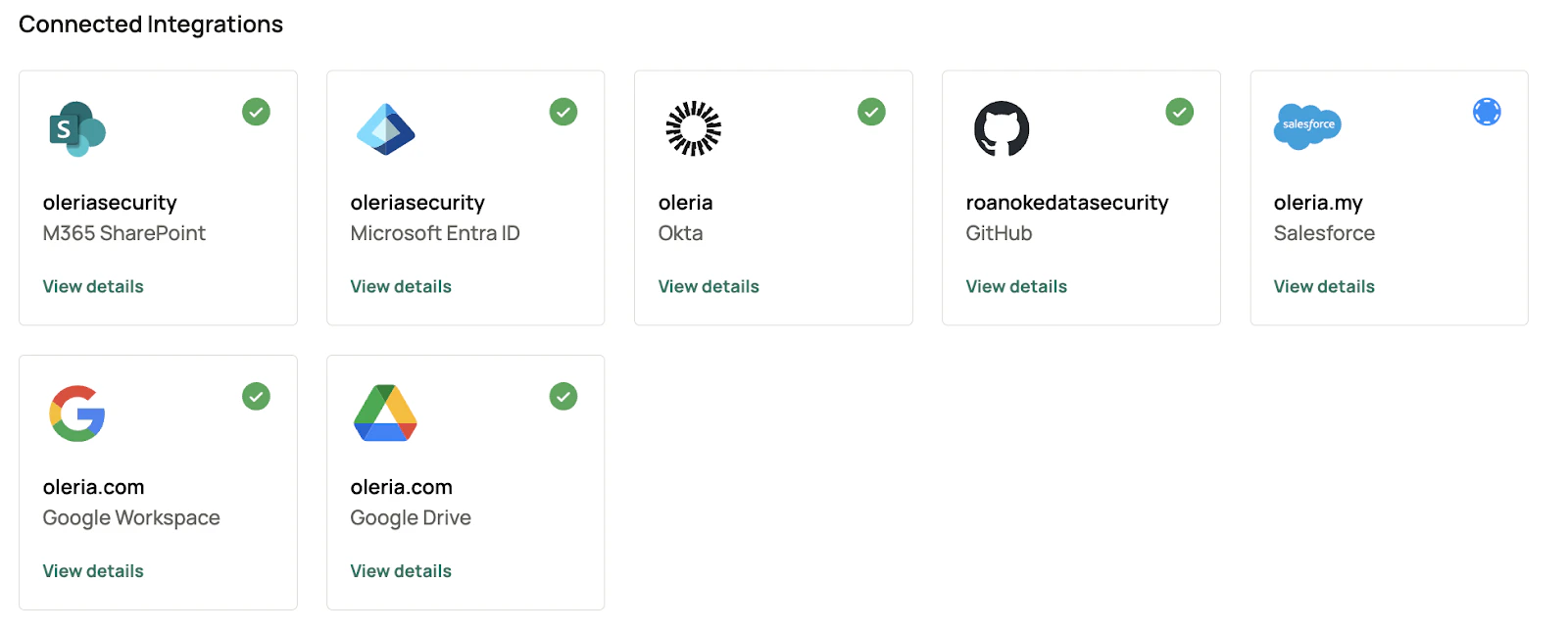
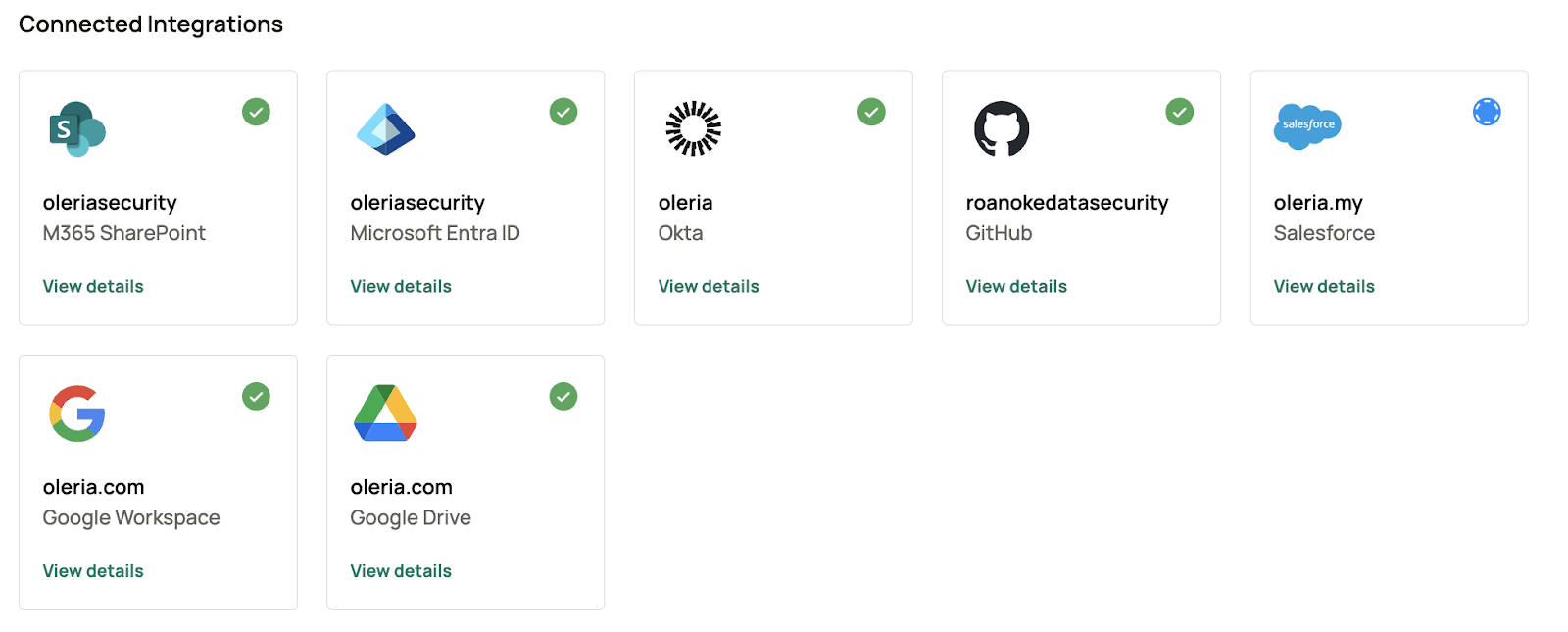
Oleria provides identity security and access management teams with visibility and intelligence into who has access to what, where they got that access, how they use it, and if they should even have it. As part of that promise, we integrate applications such as Microsoft Entra ID and M365 SharePoint into the Oleria platform. We provide multiple options for each integration and this document provides step-by-step guidance for integrating Entra ID and M365 SharePoint with your Oleria workspace.Documentation Index
Fetch the complete documentation index at: https://docs.oleria.com/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
- The user granting these permissions must have Global Admin privileges.
Integration Approaches
Oleria currently supports three approaches. Follow the one that is most appropriate for your organization.- Authenticate via Microsoft (automated configuration via OAuth)
- Client Secret Authentication (manual configuration)
- Client Certificate Authentication (manual configuration)
Authenticate via Microsoft (OAuth)
Open the integration
- Select Microsoft Entra ID to integrate Entra ID, or
-
Select Microsoft SharePoint and OneDrive to integrate Entra ID, SharePoint, and OneDrive.
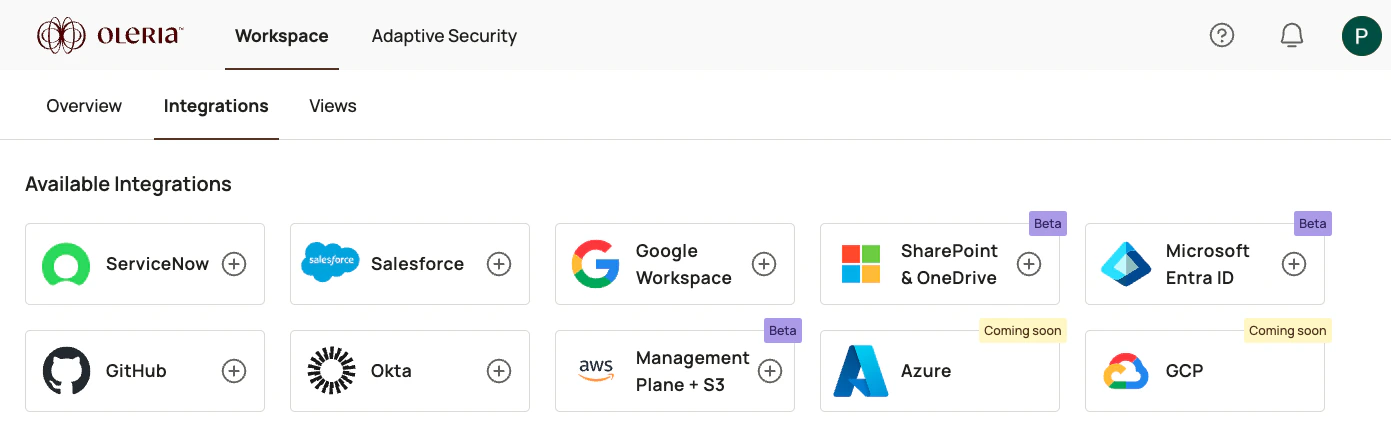
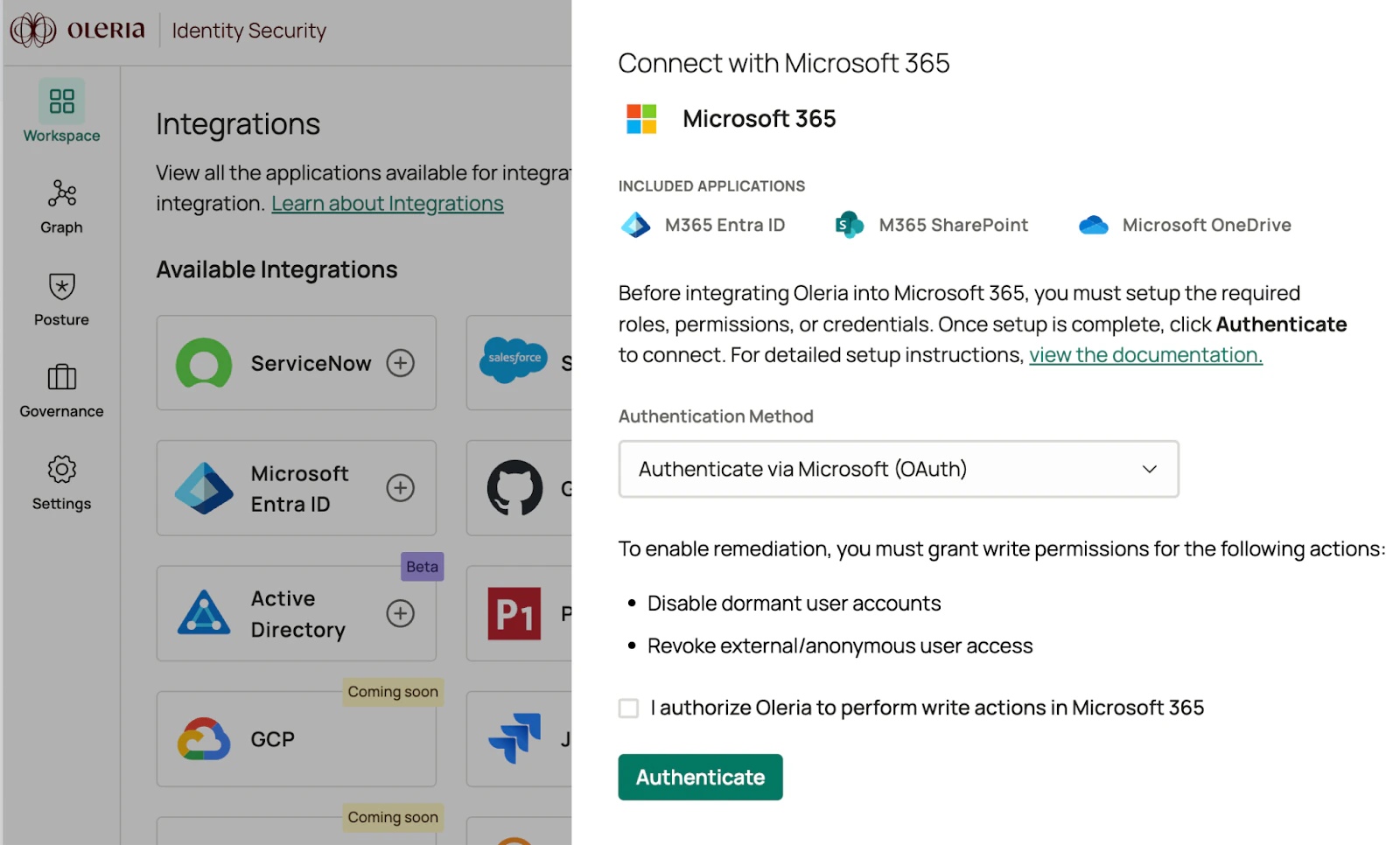
Choose permission scope
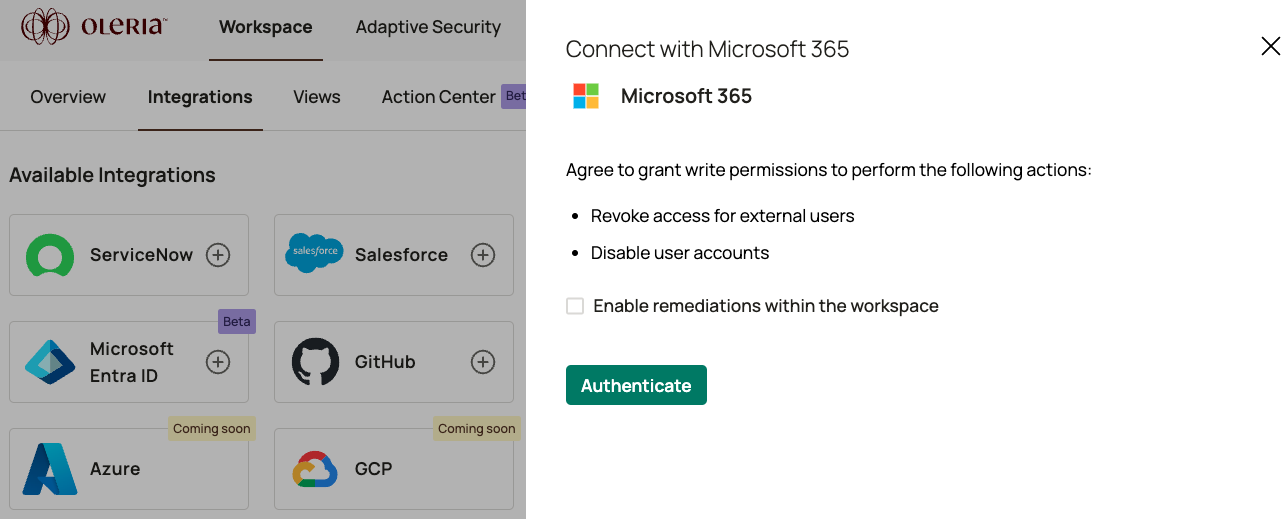
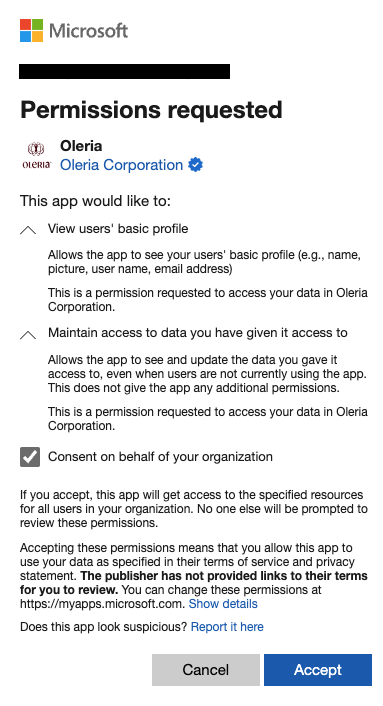
Complete the initial consent form
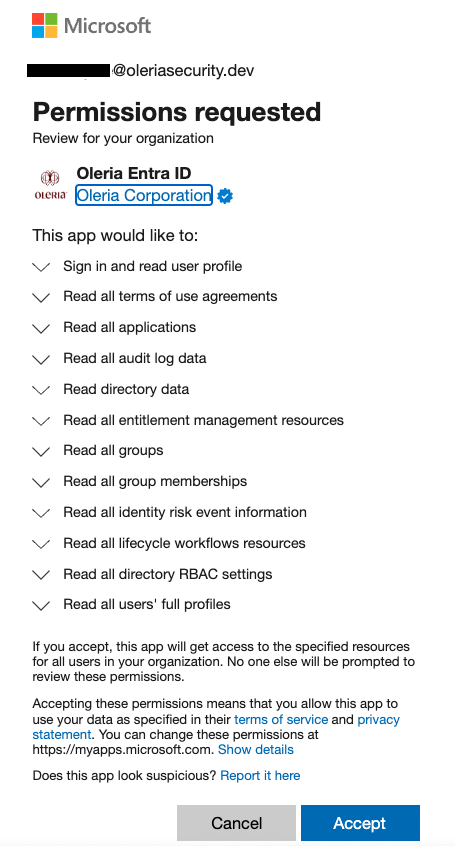
Complete the application consent form
-
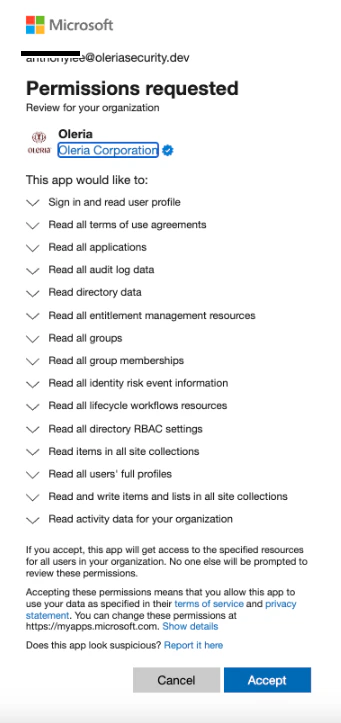
Standard read-only permissions for Entra ID integration (without optional remediations)
-
Standard read-only permissions for SharePoint and OneDrive integration (without optional remediation)
-
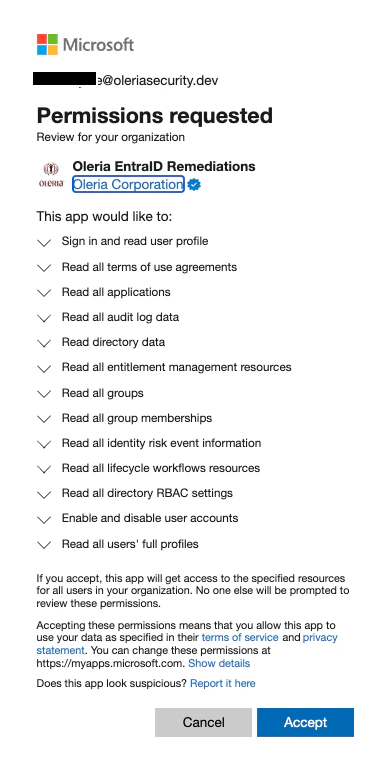
Permissions for Entra ID integration with optional remediation capabilities (includes some write permissions)
-
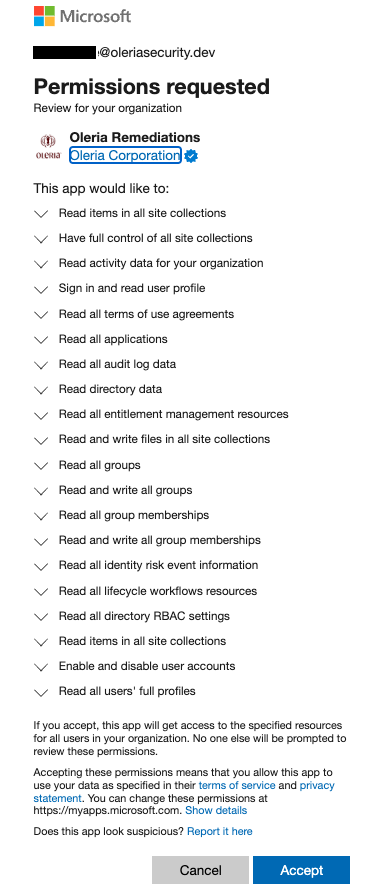
Permissions for SharePoint and OneDrive integration with optional remediation capabilities (includes some write permissions)
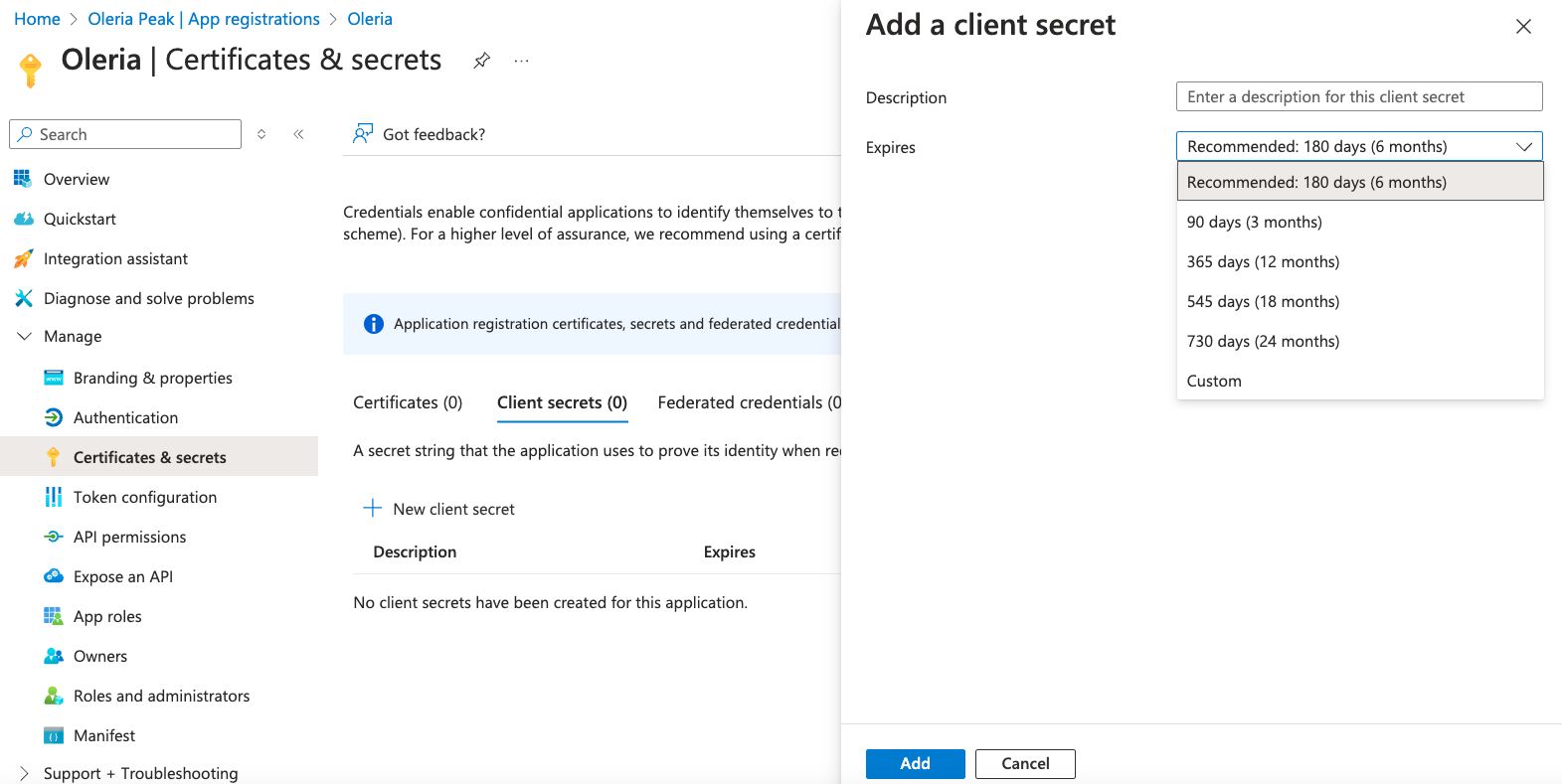
Client Secret Authentication
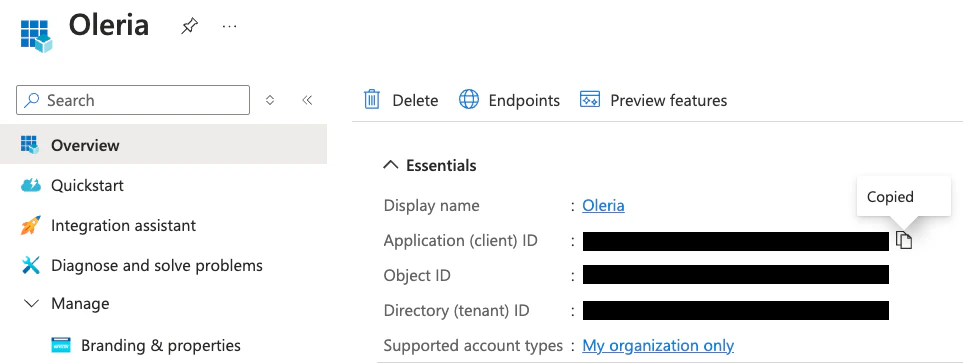
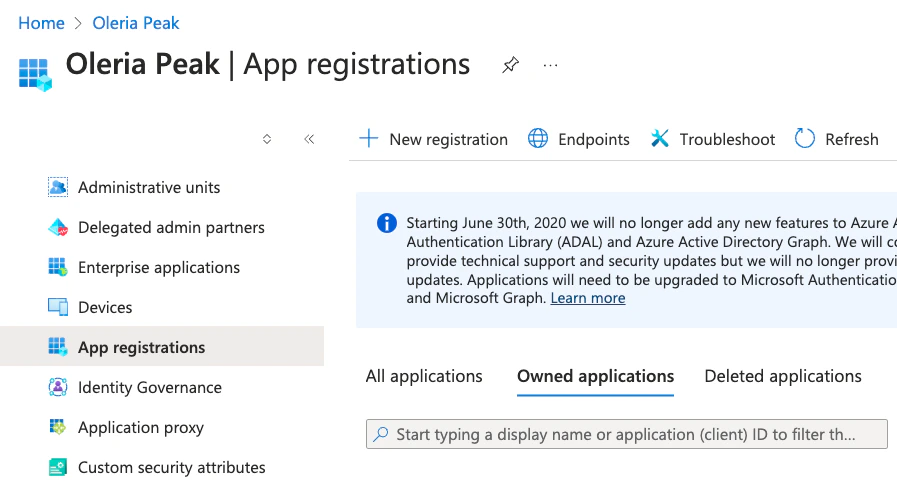
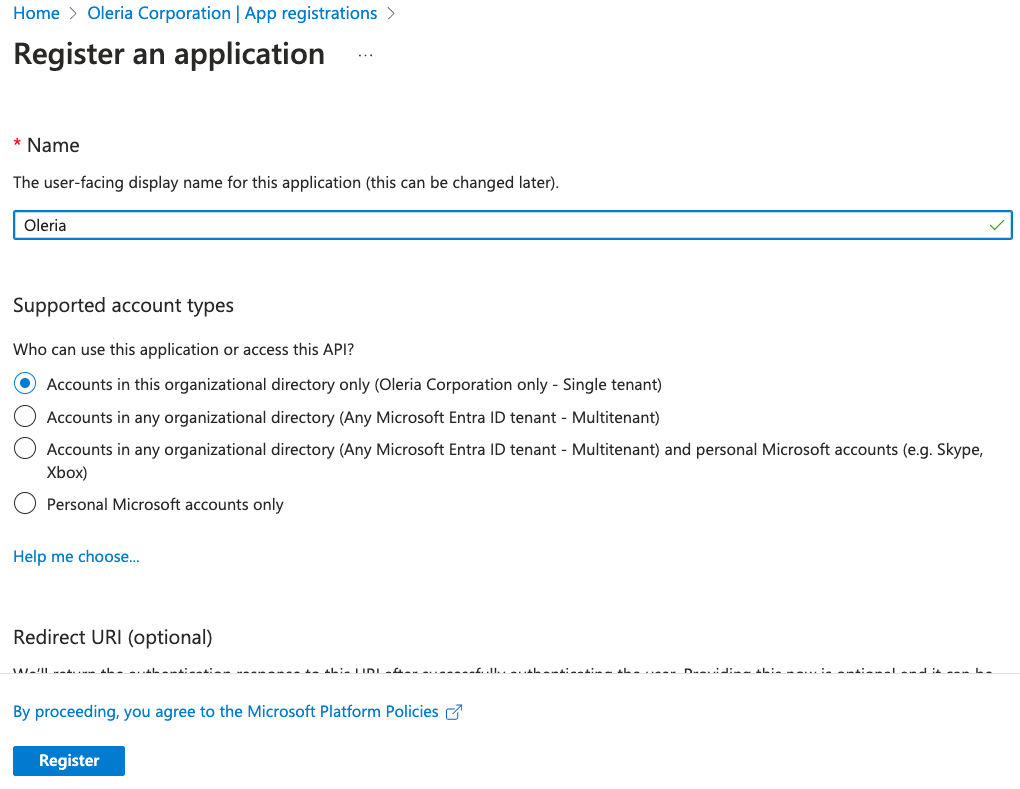
Create an app registration in Entra ID
Configure the registration
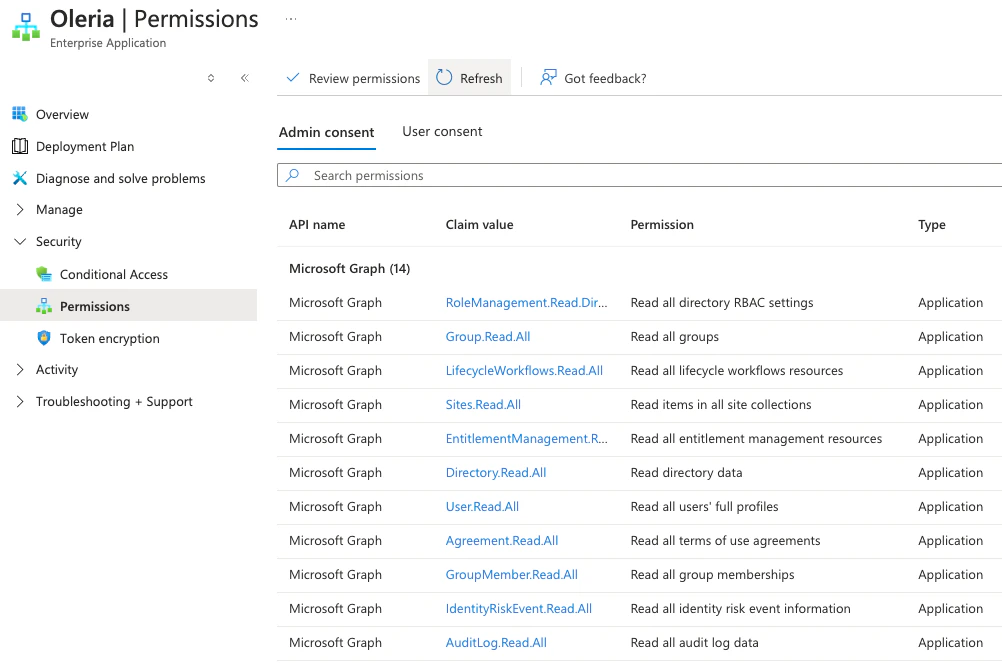
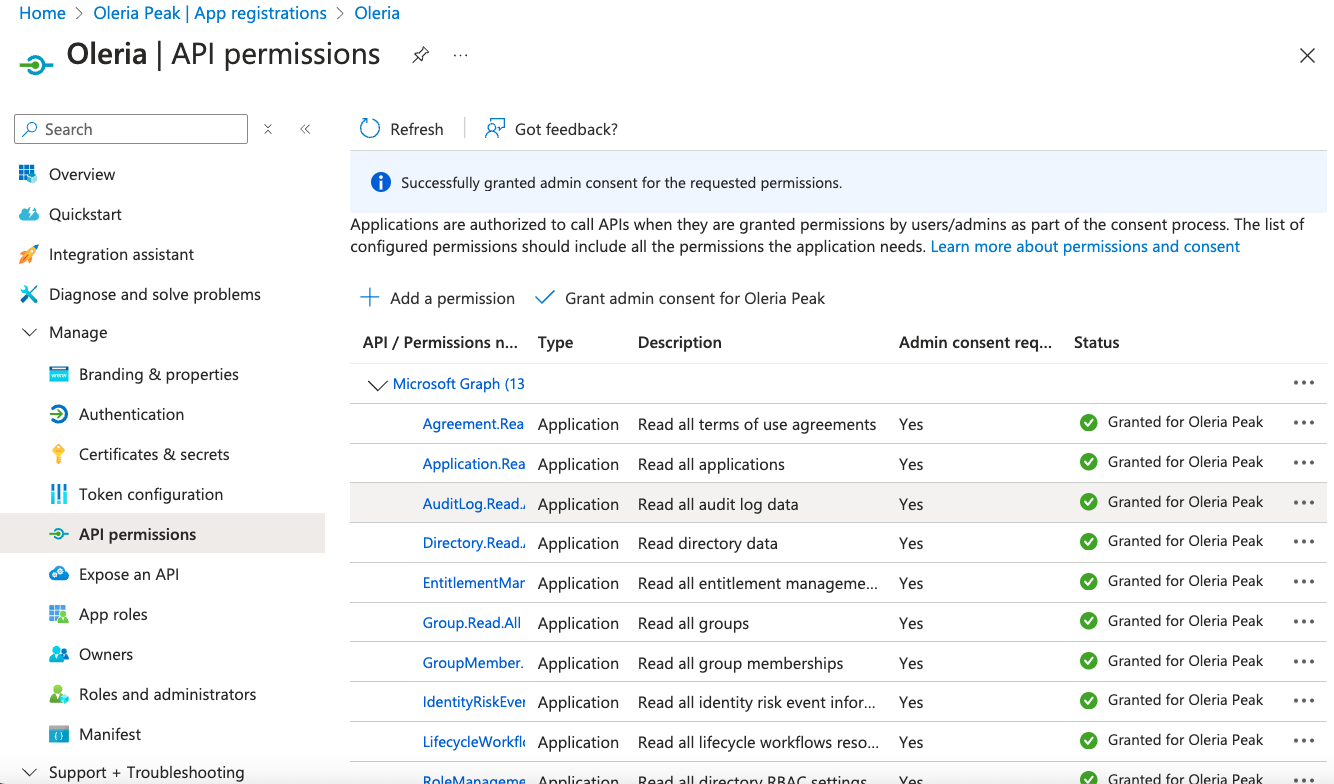
Open API permissions
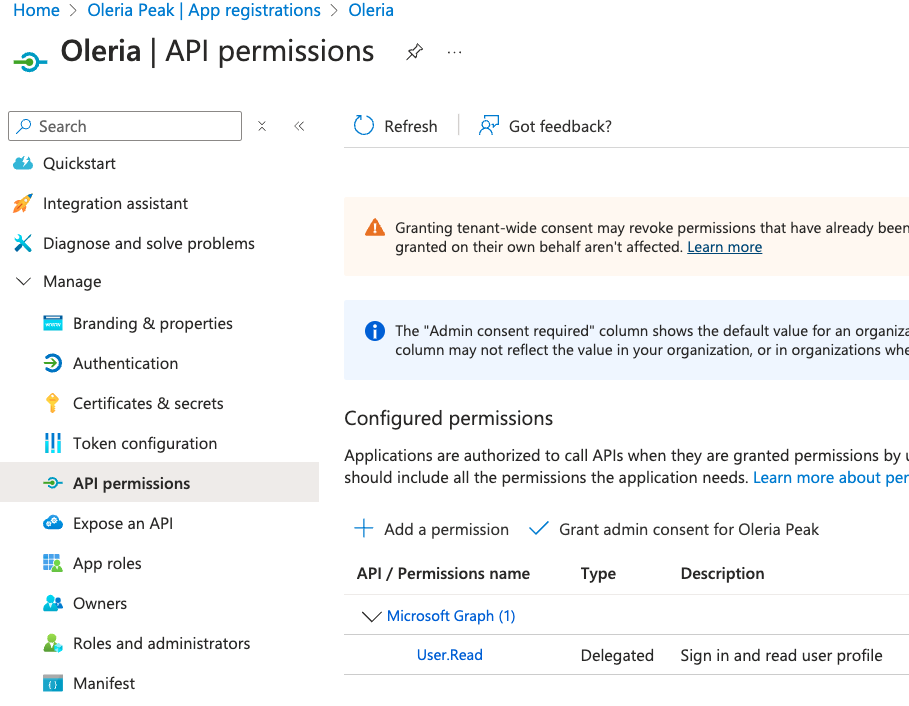
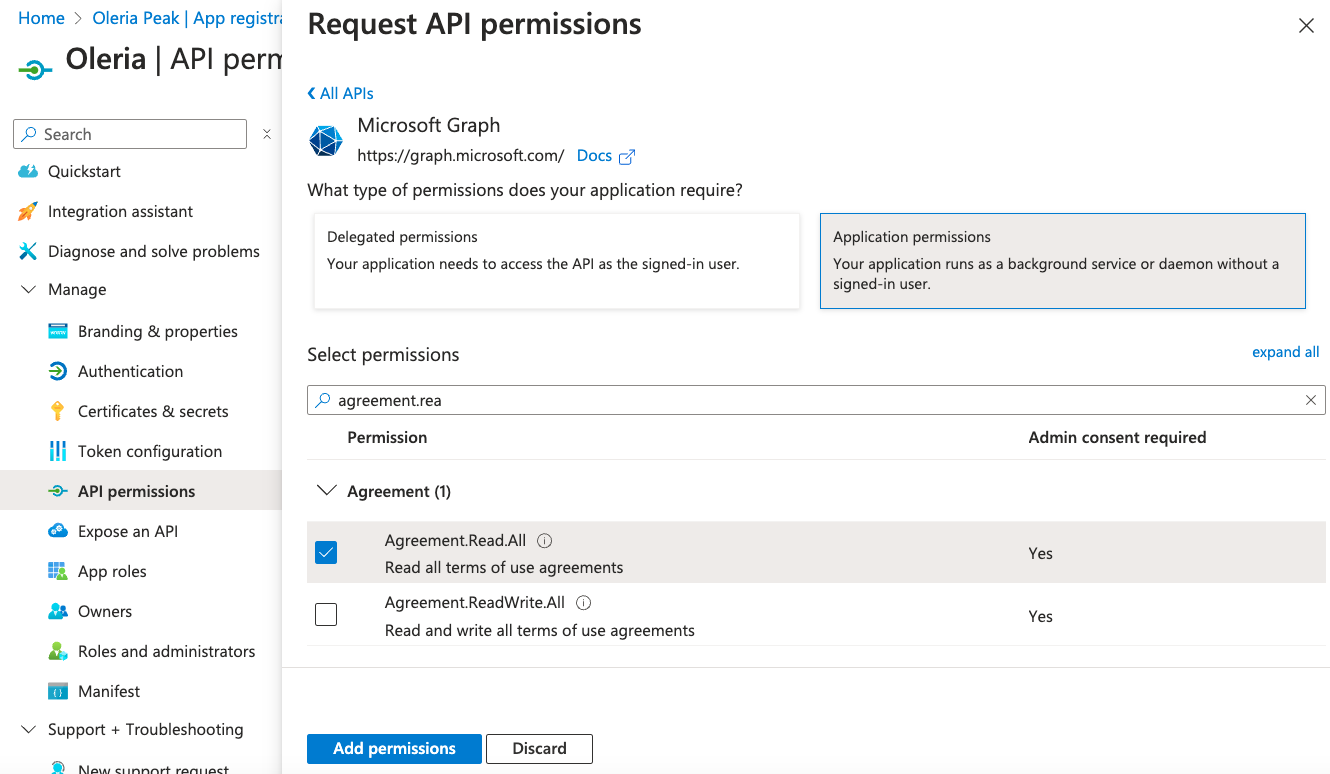
Add Microsoft Graph permissions
- Standard read-only permissions for Entra ID integration (without optional remediations)
| API / Permissions name | Type | Permission |
|---|---|---|
| Microsoft Graph (14) | ||
| Agreement.Read.All | Application | Read all terms of use agreements |
| Application.Read.All | Application | Read all applications |
| AuditLog.Read.All | Application | Read all audit log data |
| Directory.Read.All | Application | Read directory data |
| EntitlementManagement.Read.All | Application | Read all entitlement management resources |
| Group.Read.All | Application | Read all groups |
| GroupMember.Read.All | Application | Read all group memberships |
| IdentityRiskEvent.Read.All | Application | Read all identity risk event information |
| LifecycleWorkflows.Read.All | Application | Read all lifecycle workflows resources |
| Policy.read.all | Application | Read your organization’s policies |
| profile | Delegated | View users’ basic profile |
| RoleManagement.Read.Directory | Application | Read all directory RBAC settings |
| User.Read | Delegated | Sign in and read user profile |
| User.Read.All | Application | Read all users’ full profiles |
- Standard read-only permissions for SharePoint and OneDrive integration (without optional remediation)
| API / Permissions name | Type | Permission |
|---|---|---|
| Microsoft Graph (15) | ||
| Agreement.Read.All | Application | Read all terms of use agreements |
| Application.Read.All | Application | Read all applications |
| AuditLog.Read.All | Application | Read all audit log data |
| Directory.Read.All | Application | Read directory data |
| EntitlementManagement.Read.All | Application | Read all entitlement management resources |
| Group.Read.All | Application | Read all groups |
| GroupMember.Read.All | Application | Read all group memberships |
| IdentityRiskEvent.Read.All | Application | Read all identity risk event information |
| LifecycleWorkflows.Read.All | Application | Read all lifecycle workflows resources |
| Policy.read.all | Application | Read your organization’s policies |
| profile | Delegated | View users’ basic profile |
| RoleManagement.Read.Directory | Application | Read all directory RBAC settings |
| Sites.Read.All | Application | Read items in all site collections |
| User.Read | Delegated | Sign in and read user profile |
| User.Read.All | Application | Read all users’ full profiles |
| Office 365 Management APIs (1) | ||
| ActivityFeed.Read | Application | Read activity data for your organization |
| SharePoint (2) | ||
| Sites.FullControl.All | Application | Have full control of all site collections |
| Sites.Read.All | Application | Read items in all site collections |
- Permissions for Entra ID integration with optional remediation capabilities (includes some write permissions)
| API / Permissions name | Type | Permission |
|---|---|---|
| Microsoft Graph (15) | ||
| Agreement.Read.All | Application | Read all terms of use agreements |
| Application.Read.All | Application | Read all applications |
| AuditLog.Read.All | Application | Read all audit log data |
| Directory.Read.All | Application | Read directory data |
| EntitlementManagement.Read.All | Application | Read all entitlement management resources |
| Group.Read.All | Application | Read all groups |
| GroupMember.Read.All | Application | Read all group memberships |
| IdentityRiskEvent.Read.All | Application | Read all identity risk event information |
| LifecycleWorkflows.Read.All | Application | Read all lifecycle workflows resources |
| Policy.read.all | Application | Read your organization’s policies |
| profile | Delegated | View users’ basic profile |
| RoleManagement.Read.Directory | Application | Read all directory RBAC settings |
| User.EnableDisableAccount.All | Application | Enable and disable user accounts |
| User.Read | Delegated | Sign in and read user profile |
| User.Read.All | Application | Read all users’ full profiles |
- Permissions for SharePoint and OneDrive integration with optional remediation capabilities (includes some write permissions)
| API / Permissions name | Type | Permission |
|---|---|---|
| Microsoft Graph (19) | ||
| Agreement.Read.All | Application | Read all terms of use agreements |
| Application.Read.All | Application | Read all applications |
| AuditLog.Read.All | Application | Read all audit log data |
| Directory.Read.All | Application | Read directory data |
| EntitlementManagement.Read.All | Application | Read all entitlement management resources |
| Files.ReadWrite.All | Application | Read and write files in all site collections |
| Group.Read.All | Application | Read all groups |
| Groups.ReadWrite.All | Application | Read and write all groups |
| GroupMember.Read.All | Application | Read all group memberships |
| GroupMember.ReadWrite.All | Application | Read and write all group memberships |
| IdentityRiskEvent.Read.All | Application | Read all identity risk event information |
| LifecycleWorkflows.Read.All | Application | Read all lifecycle workflows resources |
| Policy.read.all | Application | Read your organization’s policies |
| profile | Delegated | View users’ basic profile |
| RoleManagement.Read.Directory | Application | Read all directory RBAC settings |
| Sites.Read.All | Application | Read items in all site collections |
| User.EnableDisableAccount.All | Application | Enable and disable user accounts |
| User.Read | Delegated | Sign in and read user profile |
| User.Read.All | Application | Read all users’ full profiles |
| Office 365 Management APIs (1) | ||
| ActivityFeed.Read | Application | Read activity data for your organization |
| SharePoint (2) | ||
| Sites.FullControl.All | Application | Have full control of all site collections |
| Sites.Read.All | Application | Read items in all site collections |
Grant admin consent
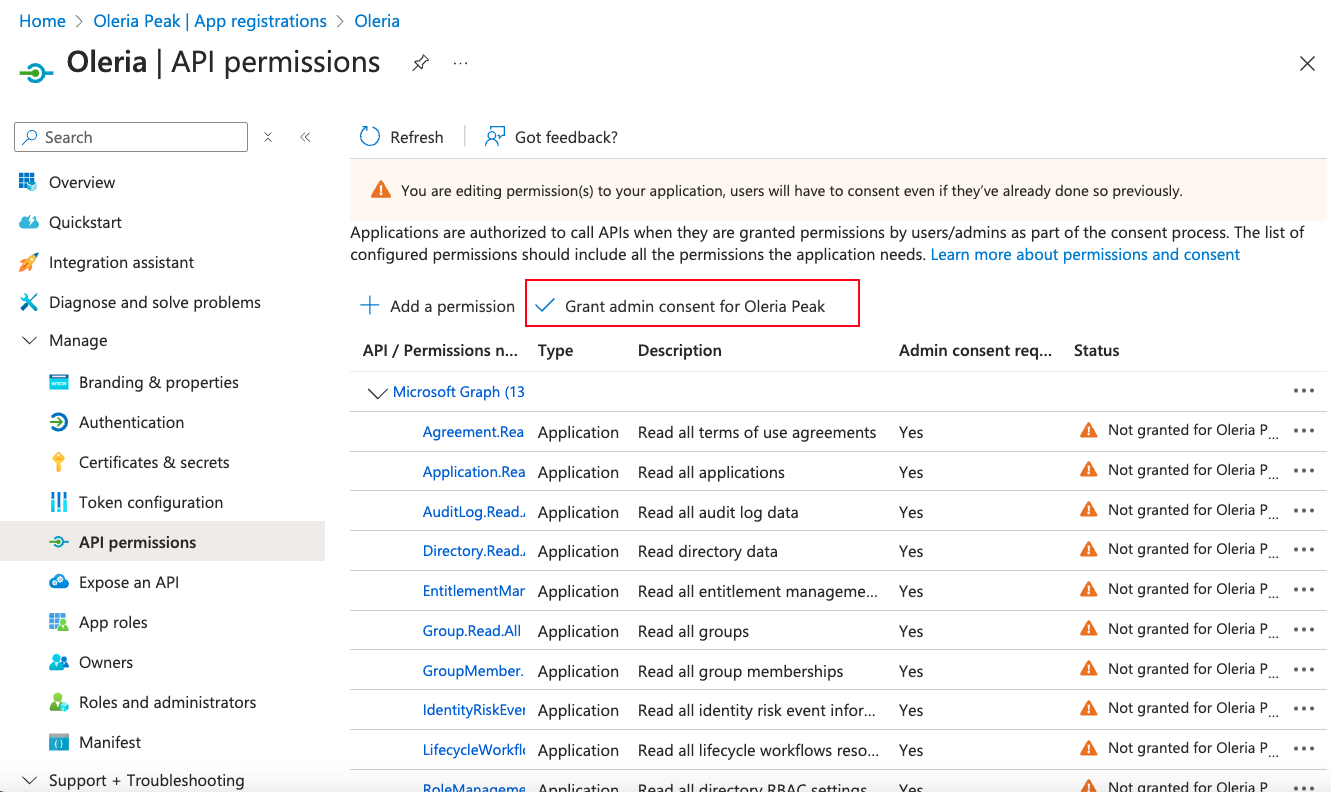
Confirm admin consent
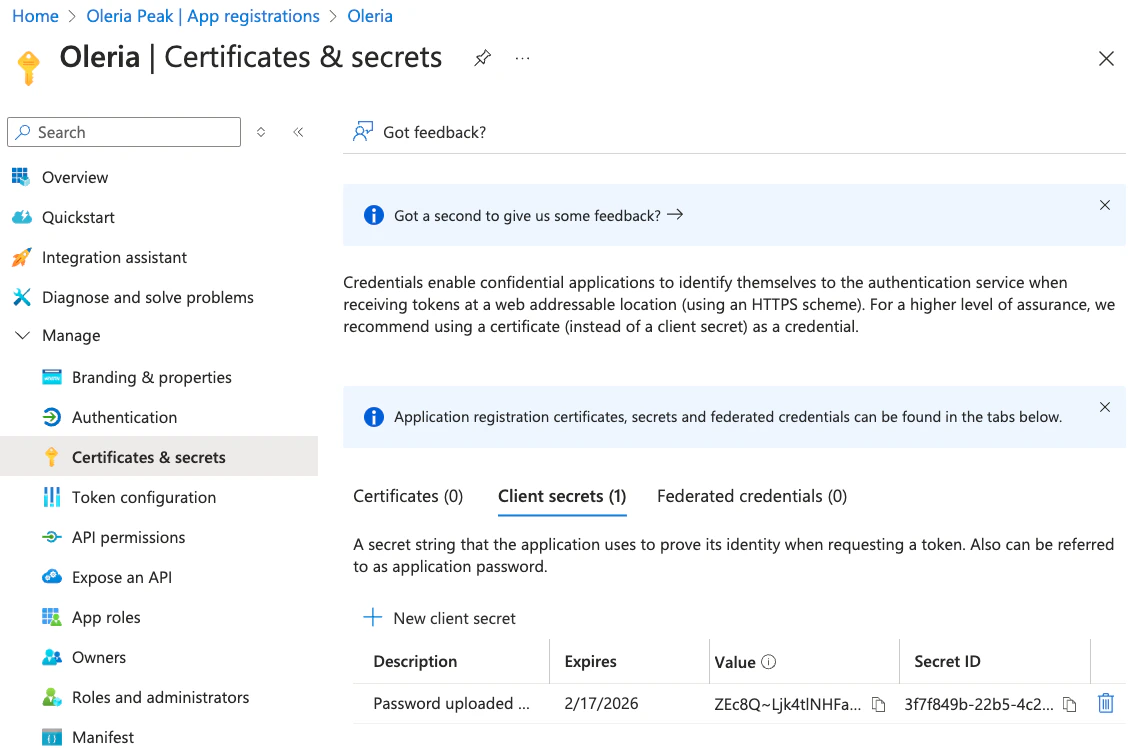
Copy the client secret value
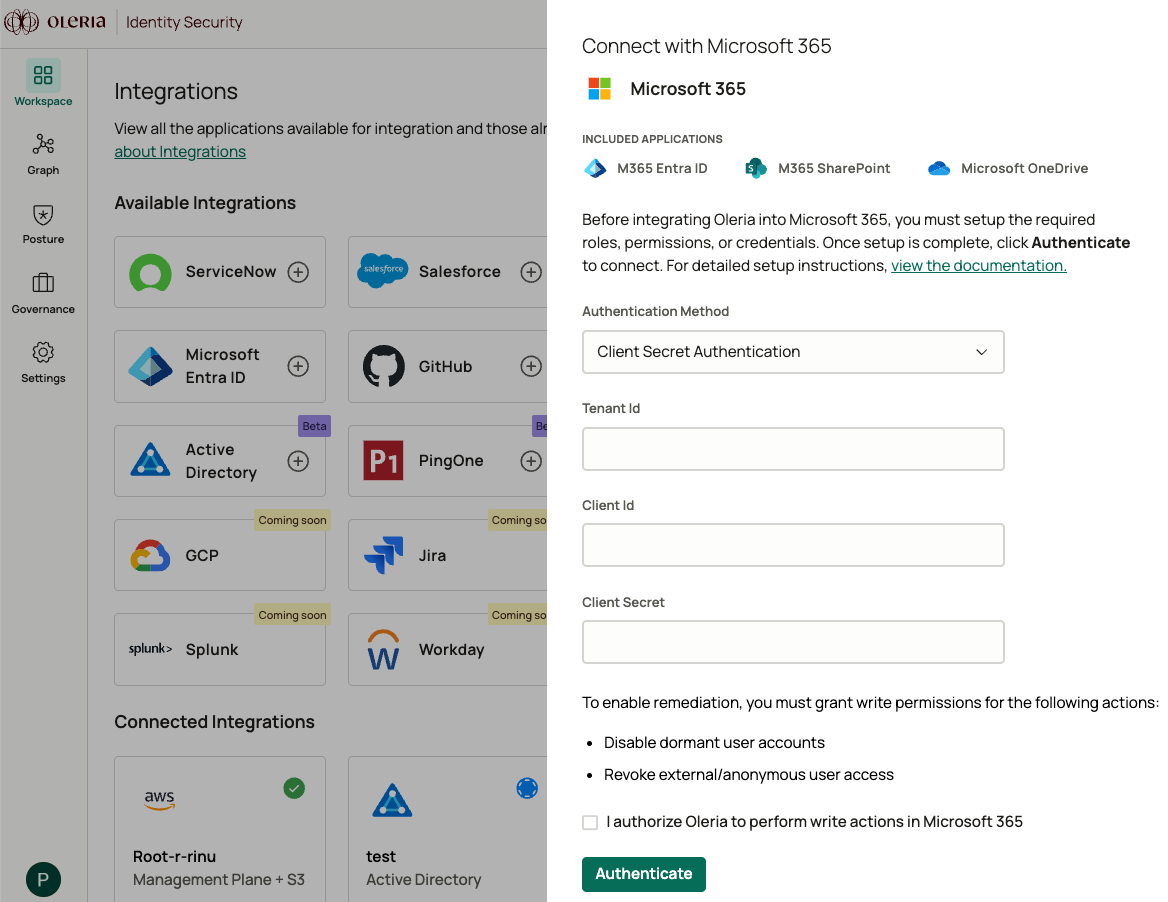
Open the integration in Oleria
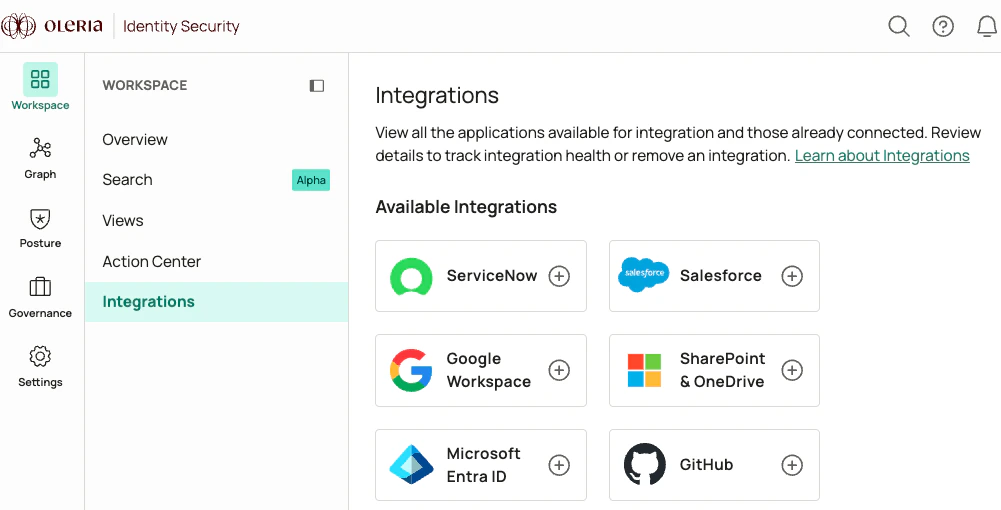
Authenticate with Client Secret
Client Certificate Authentication
Client certificate authentication uses a certificate uploaded to your Oleria app registration in Entra ID and a base64-encoded private key stored by Oleria. Use this method when your security policy requires certificate-based service principal authentication instead of a client secret.Prepare your certificate files
certificate.pem- the public certificate in PEM formatprivate_key.txt- the matching unencrypted private key in PEM formatcertificate_chain.txt- the intermediate certificate chain in PEM format
New-SelfSignedCertificate on Windows) and export it in the formats above.private_key.txt is passphrase-protected, decrypt it first with openssl rsa -in private_key.txt -out private_key.txt (or the equivalent for your key type) before continuing.Generate the base64-encoded private key
- macOS or Linux
- Windows (PowerShell)
base64_generate_cert.pem is the value you will paste into Oleria in the final step.Upload the certificate to Entra ID
certificate.pem.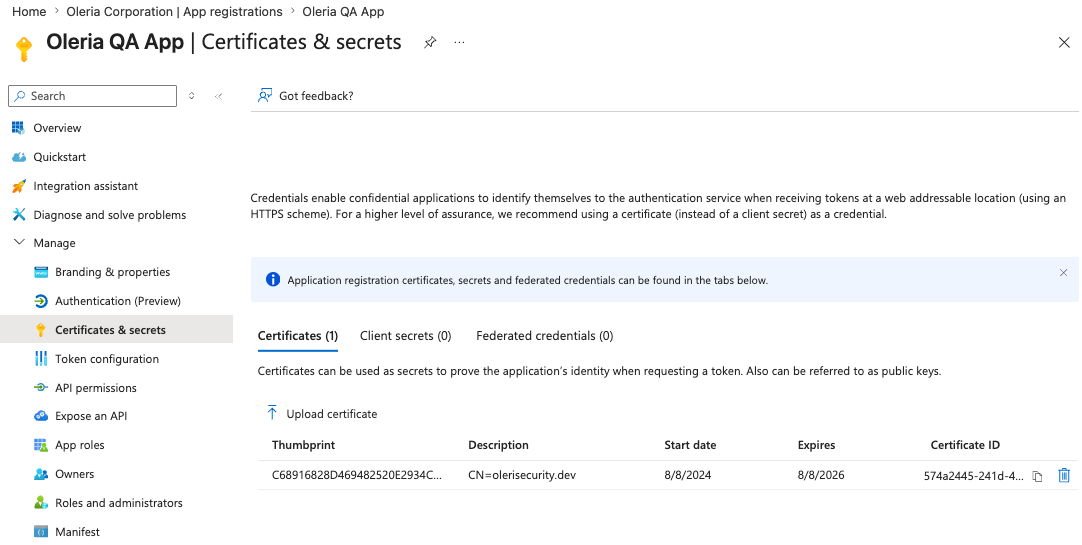
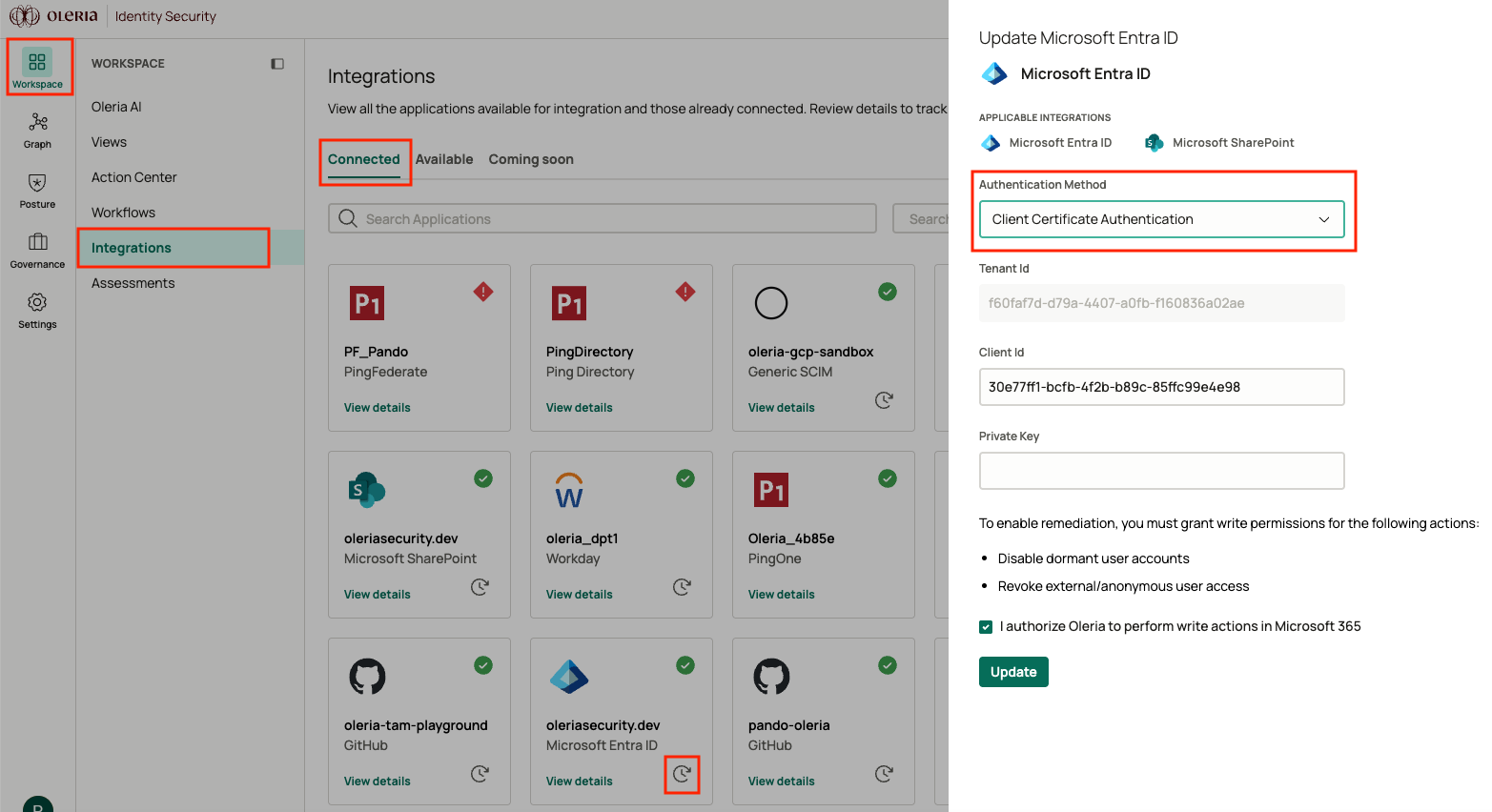
Open the integration in Oleria
- For a new integration, select Microsoft Entra ID or Microsoft SharePoint and OneDrive to open the side panel.
- To migrate an existing integration from client secret to client certificate, select Connected, then select the edit icon on your Entra ID integration to open the side panel.
Authenticate with the client certificate
| Field | Notes |
|---|---|
| Tenant ID | Your Directory (tenant) ID from the app registration overview. |
| Client ID | Your Application (client) ID from the app registration overview. |
| Private Key | The contents of base64_generate_cert.pem from the previous step. |
Clean up generated files
generated_cert.pem and base64_generate_cert.pem both contain the unencrypted private key inline. Delete them from the working directory now that the integration is connected. Your original certificate.pem, certificate_chain.txt, and private_key.txt files are unchanged and can stay in your existing key store.- macOS or Linux
- Windows (PowerShell)
history -c on Bash or Zsh, Clear-History on PowerShell.How Oleria handles the private key
The Private Key field in the integration form is masked to prevent shoulder-surfing during entry. The value is transmitted to Oleria over TLS and persisted in AWS Secrets Manager, which provides encryption at rest with KMS-managed keys and audit logging on every access. Access to the secret is scoped to the Oleria service that authenticates to Entra ID; no human operator and no other Oleria service can read it. Oleria does not write the private key to application logs, databases, or temporary files. It is read from AWS Secrets Manager into process memory only when authenticating to Entra ID, and is held in memory only for the duration of that authentication.Check the Oleria App in Your Entra ID Instance
Find the Oleria app in Enterprise applications
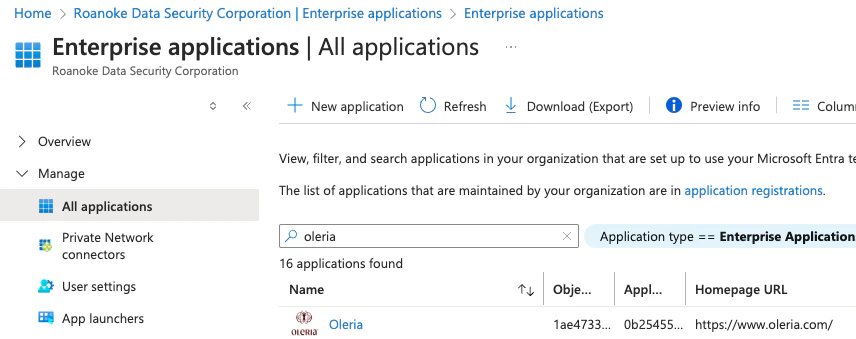
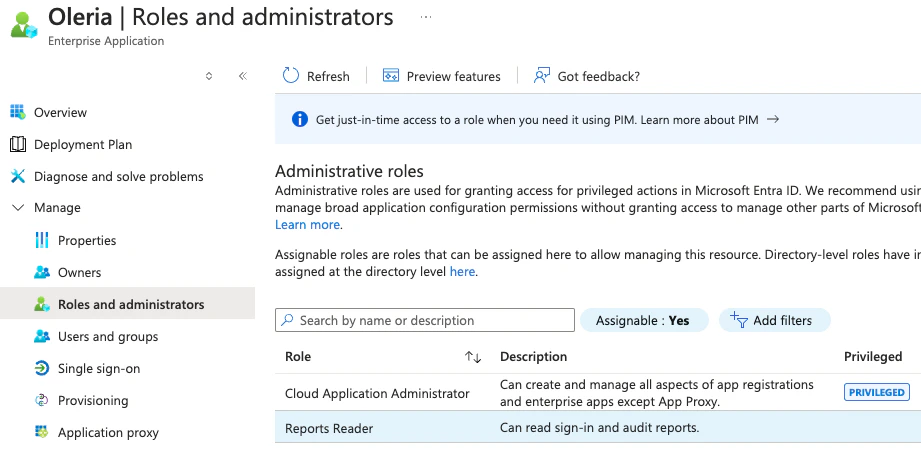
View assigned roles
- Cloud Application Administrator
-
Report Reader